Platform
PRODUCTS
INFRASTRUCTURE
Use Cases
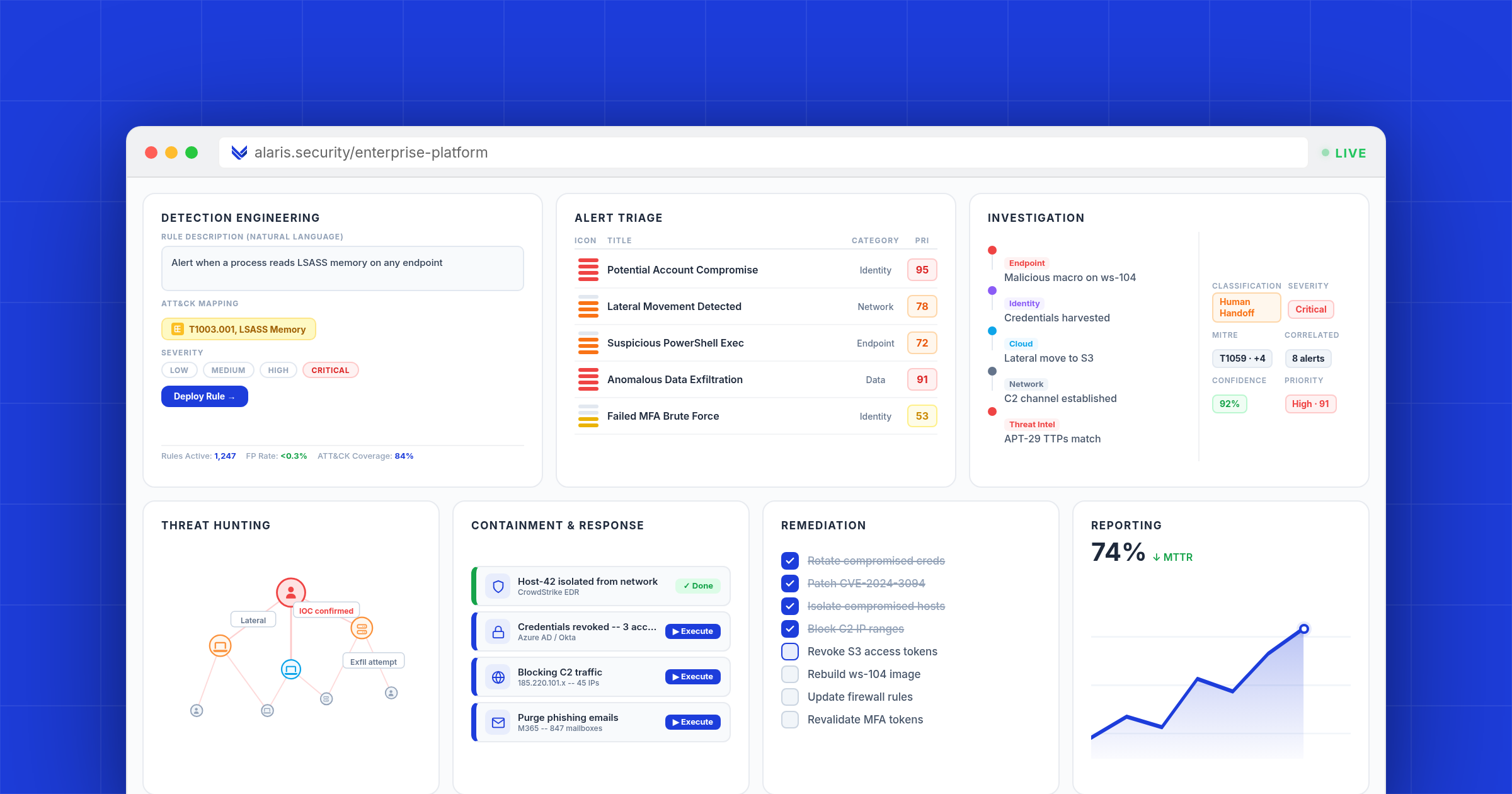
AUTONOMOUS SECURITY OPERATIONS
Detection EngineeringNEW
Custom detection rules & management
Autonomous Alert Analysis
AI-driven alert triage & analysis
Human + AI Investigations
Full-context investigations at scale
Autonomous Threat Hunting
Proactive, continuous threat discovery
Response & Recovery
Automated containment & remediation
Compliance Reporting
Automated audit readiness & reporting
EXTENDED USE CASES
Resources
Compare. Evaluate. Decide.
In-depth comparisons and analysis to help security teams cut through vendor noise and make confident decisions.
What is Autonomous Security Operations (ASO)?
The definitive guide to the category that brings full autonomy to your entire security operations function. One platform, six stages, full autonomy.
We're Giving Script Kiddies Nuclear Weapons
AI is democratizing offensive capabilities at an unprecedented rate. What happens when sophisticated attack tooling is available to anyone with a prompt?
ASO vs AI SOC
"AI SOC" has become a catch-all that covers everything from a chatbot bolted onto your SIEM to a fully autonomous platform. Anton Chuvakin drew the line years ago. Here is why architecture, not branding, determines whether AI actually transforms security operations.
Is This the Future of Autonomous Security Operations (ASO)?
Security operations has evolved from manual triage to AI copilots. The next frontier is full autonomy. Here's what ASO looks like and why it matters.
Anatomy of a Supply Chain Breach: LiteLLM, TeamPCP, and 4TB of Stolen Data
A technical breakdown of the LiteLLM supply chain compromise that led to the exfiltration of 4TB of data from a $10 billion AI startup. We analyze the three-stage backdoor, map the full kill chain to MITRE ATT&CK, and document every indicator of compromise and detection opportunity that was missed.
A Statement on Project Glasswing
On April 7, an AI model found a 27-year-old vulnerability in minutes. Thousands more followed. The world just changed, and most of the security industry is not ready for what comes next.