I've spent the last four years in rooms with CISOs, security leaders, and the teams who run security operations. Over the course of more than a hundred conversations, from Fortune 500 companies to mid-market firms trying to build their security function from scratch, I kept hearing the same things. Our tools don't talk to each other. My team spends their whole day swiveling between platforms. We can't keep up with the volume. The stack we bought three years ago is already outdated. Different words, different organizations, same structural problem showing up everywhere regardless of size or budget.
Key takeaways:
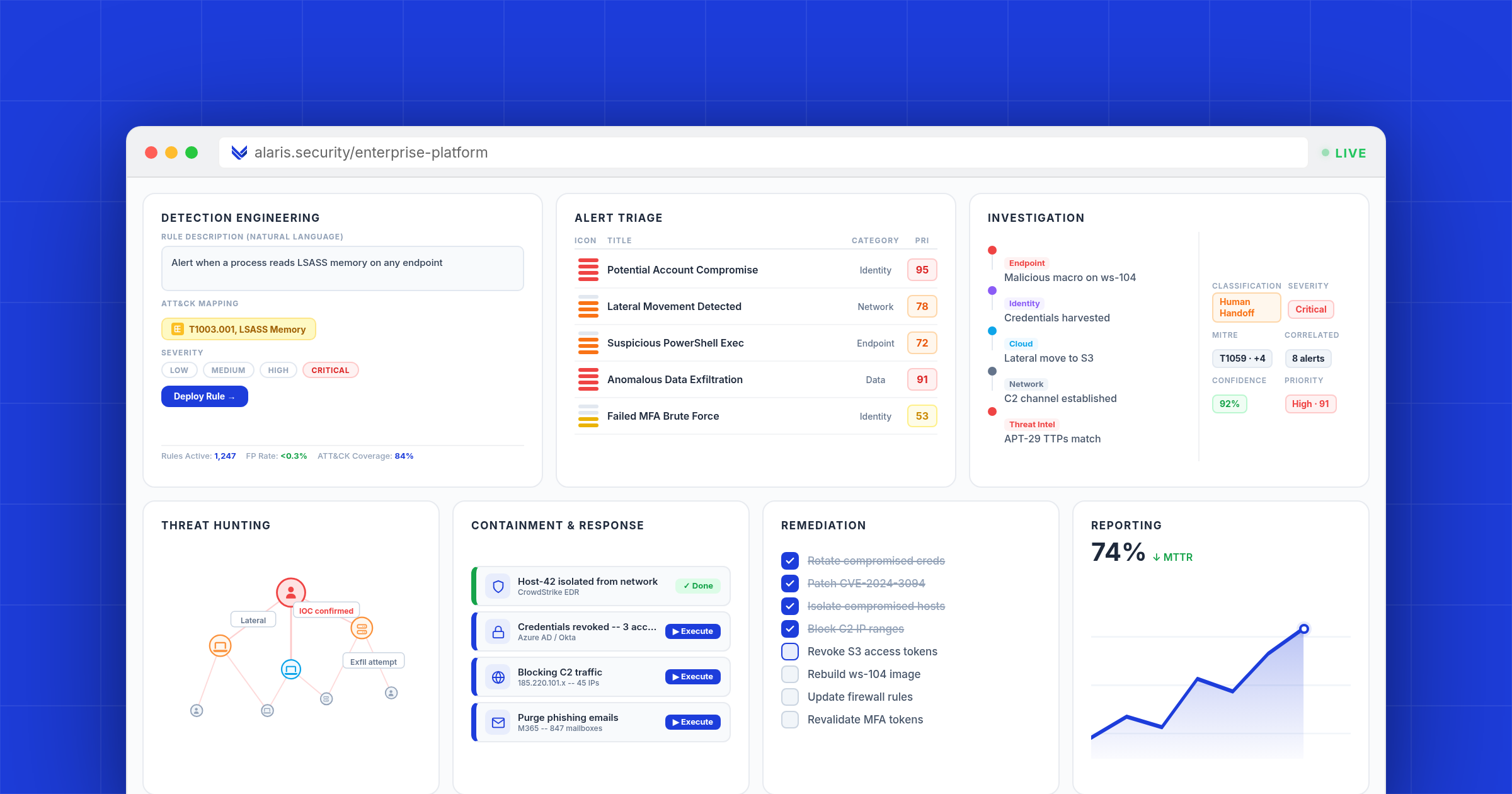
- Autonomous Security Operations (ASO) is a new category: one platform covering all seven stages of security operations with full autonomy.
- The three defining traits of ASO are unified architecture, end-to-end autonomy, and full operational scope across all seven stages.
- ASO does not eliminate security professionals. It changes what they do, shifting the role from operating the toolchain to governing outcomes.
- ASO works with your existing stack. It is not a rip-and-replace proposition.
The Problem
At a roundtable I hosted at RSA, one CISO described the workflow: SIEM to XDR to SOAR to ticketing system to spreadsheet. Five tools, five context switches, and an analyst serving as the glue between all of them. The most expensive and hardest-to-hire people in his organization, spending more time operating the toolchain than defending the company.
That is not a tooling problem. It is an architecture problem. And no amount of incremental improvement to any single category will fix it.
Autonomous Security Operations (ASO) is the new category built to solve it. One platform that covers all seven stages of security operations with full autonomy. ASO works with your existing tools but changes what they require of your team. The human sets the strategy. The platform operates.
The Core Idea
Think about a self-driving car. The human doesn't operate the steering, brakes, gas, and GPS separately. The human sets the destination. The car handles the driving. Now think about your SOC. Nothing happens unless a human initiates it. An analyst monitors one tool, switches to another to investigate, opens a third to trigger a playbook, jumps to a fourth to document findings. A thousand micro-decisions per shift, and the human is the middleware connecting all of it.
ASO is the self-driving car for security operations. It doesn't eliminate the human. It changes the human's role. The human sets the destination: here is our risk tolerance, here are our priorities, here is what matters. The platform handles the driving.
The Seven Stages of Security Operations
Security operations is not one function. It is seven distinct stages, each with its own requirements, workflows, and failure modes. Every SOC performs all seven, whether they have purpose-built tools for each stage or not. The gaps between stages are where incidents get worse, response times balloon, and analysts burn out.
ASO is the first category that covers all seven in a single platform, autonomously.
- Detection Engineering: continuously engineers and refines detections based on the threat environment, no manual rule writing
- Alert Triage: autonomously determines what is real, what is noise, and what needs escalation, 100% of alert volume, 24/7
- Investigation: correlates evidence across the full environment and delivers analyst-grade investigation reports
- Threat Hunting: hunts continuously, operationalizing threat intelligence in real time without waiting for an alert
- Containment & Response: executes containment actions and coordinates the full incident response workflow autonomously
- Remediation: identifies and addresses the underlying vulnerability or misconfiguration that allowed the breach
- Reporting: generates reports continuously, audit-ready, regulator-ready, board-ready
Most tools on the market today started by covering one or two of these stages. The best are expanding to four or five. But none were built from the ground up to cover all seven as a single, unified platform. They are assembling coverage by bolting on new agents, acquiring capabilities, or layering AI onto architectures that were never designed for end-to-end autonomy. That architectural gap is where attacks succeed, analysts burn out, and CISOs lose sleep.
Why the Current Architecture is Failing
The average enterprise SOC runs five or more categories of security tools. Each tool was best-in-class when it was purchased. Each solves a real problem. And together, they create a system where the analyst is the integration layer.
I watched this play out in real time during an engagement with a large enterprise security team. They had invested millions in their stack. Every tool was top-tier. And their mean time from alert to containment was still measured in hours, not minutes. When I asked why, the answer was always the same: the tools don't connect.
An analyst sees an alert in the SIEM, pivots to the XDR for context, opens a case in the ticketing system, checks threat intelligence in a separate feed, triggers a containment action through the SOAR, and writes up the findings in a spreadsheet. That workflow takes 30 to 90 minutes for a single alert. Meanwhile, the attacker has been inside the environment for the entire duration.
The industry's response has been to add more automation within each tool. SIEMs got smarter correlation. XDRs added automated response. SOARs expanded their playbook libraries. But each improvement only optimizes one stage. The handoffs between stages remain manual.
“His team has the tools, but the tools don't have each other. They've stacked automation on top of fragmentation and expected it to produce coherence. It doesn't.”
Security leader, CactusCon 2026
This is why the answer is not a better tool. The answer is a different architecture. One platform that covers the entire workflow, end to end, with no handoffs, no context switching, and no human middleware required.
What Makes ASO Different from Everything Else
ASO is not an improvement to an existing category. It is a new one. Three things define it, and the order matters.
Unified Architecture
This is the big one. ASO is a single platform where every stage shares context, shares reasoning, and operates as one system. Not five tools stitched together. Not separate AI agents each handling one function. One system. The reason this matters more than anything else: if the architecture is fragmented, nothing you build on top of it will feel unified. You can bolt autonomy onto a broken stack, and you'll get a faster broken stack. We've watched the industry try this for years. It doesn't work.
End-to-End Autonomy
ASO doesn't wait for a human to move context between stages. It operates continuously, making decisions, taking actions, and producing outputs across the entire lifecycle. But here is what gets misunderstood about autonomy: it does not mean humans are out of the picture. Humans are critical. They set the strategy, define the boundaries, and make the judgment calls that require business context. What changes is what they spend their time on. And the analyst stays in control. If you want 100% of operations running without input, you can do that. If you want the platform to handle 50% and escalate the rest, you can do that too. The dial is yours.
Full Operational Scope
Security operations is not a single task. It is a flow. Detection feeds triage. Triage feeds investigation. Investigation feeds containment. Containment feeds remediation. Remediation feeds the next detection. If you automate five of those stages but leave two manual, the flow breaks. The analyst is still stuck in the middle, carrying context across the gap. You cannot call something autonomous if it only covers part of the operation. ASO covers all seven stages because that is what "security operations" actually means. All of it. End to end.
Other categories have one or two of these. Some are expanding. But nobody has all three working together: unified architecture, end-to-end autonomy, and full scope.
How ASO Compares to the Market
The industry is moving in this direction, which validates the thesis. But not everyone means the same thing when they use the word "autonomous."
- SIEM: log collection and correlation, no autonomy, no response, no hunting, no remediation
- SOAR: playbook automation, partial autonomy with static logic, breaks on novel threats and requires engineers
- XDR: detection and response, partial autonomy, no detection engineering, no reporting, no hunting
- AI SOC: alert triage and investigation, high autonomy for covered stages, but assembled from separate agents with no unified platform covering all seven
- ASO: all seven stages, full autonomy, the complete security operations function
Several of the largest platform vendors in cybersecurity are adding AI features to their existing products. They have broad portfolios and massive customer bases, but their architecture is still built on the assumption that a human connects the stages. Adding AI to a legacy architecture does not produce autonomy. It produces a slightly faster version of the same broken workflow.
A wave of startups proved that AI can handle alert triage autonomously. That was a breakthrough. The best of them are now expanding: adding threat hunting agents, containment actions, detection tuning. Real progress. But expanding from two stages to five by adding separate agents onto existing toolchains is not the same as building one platform for all seven from the ground up.
The gap nobody owns: full scope, full autonomy, unified architecture. That is ASO.
How ASO Works With Your Existing Stack
ASO is not a rip-and-replace proposition. It works with your existing SIEM, XDR, identity provider, and cloud environment. But where your current stack requires an analyst to carry context between systems and manually execute each stage of the workflow, ASO handles that connective tissue autonomously.
Over time, organizations may find that ASO absorbs functions they previously needed separate products for. If you want to use ASO as your primary detection engine, you can. If you want to keep your existing SIEM and let ASO handle everything downstream, you can do that too.
The CISOs I've spoken with don't want to be told they have to throw out their entire stack on day one. They want to see the platform work, build trust in its decisions, and expand its scope at their own pace. That's how adoption should work.
What ASO Means for Security Teams
ASO does not eliminate security professionals. It changes what they do.
Today, the majority of a security analyst's time is spent on operational mechanics: writing detection rules, triaging alerts, correlating data across tools, documenting incidents, compiling reports. The actual thinking, understanding risk, making strategic decisions, anticipating threats, gets squeezed into whatever time is left over.
“My best analysts, the people I trust most with the hardest problems, spend 80% of their time on work a machine should be doing. I can't hire fast enough to close the gap, and even if I could, the new hires would spend their first year learning the toolchain, not defending the organization.”
Security leader, Major healthcare organization
ASO inverts that ratio. When the platform handles the operational execution, the human focuses on what humans are best at: judgment, strategy, and context that only comes from understanding the business.
A CISO running an ASO platform is not managing a team of tool operators. They are overseeing an autonomous system that reports its findings, explains its decisions, and executes within the boundaries they define. The role shifts from managing workflows to governing outcomes.
Why Now
Three things converged that made ASO not just possible, but necessary.
First, threat actors got dramatically faster. Government systems, city infrastructure, critical services: breaches are hitting organizations that were supposed to be well defended. People with no real hacking skills are posting their exploits on social media, walking through systems that were left exposed. When the barrier to attack drops that low and the speed of compromise accelerates that fast, a security model that relies on humans manually connecting five tools cannot keep up. The math doesn't work.
Second, AI reached the point where it can actually make security decisions autonomously. Not copilot suggestions. Real decisions. Purpose-built reasoning systems that process the full context of a security event and produce outcomes that match or exceed what a trained analyst would do. This was not possible three years ago.
Third, the talent gap became permanent. The cybersecurity industry is short 4.8 million people, according to ISC2. By 2025, 88% of organizations had experienced a significant cybersecurity event because of skills shortages. You cannot hire your way out of this. The SOC model that assumes abundant, affordable human analysts is over.
How We Got Here
ASO did not start as a thesis. It started as a pattern.
For years, through my work advising enterprises on their security posture, I talked to CISOs at conferences, at dinners, in private roundtables. From events at RSA to smaller gatherings with security leaders from major healthcare systems, universities, and technology companies, the same frustrations kept surfacing. The pattern was everywhere.
In 2024, after hundreds of these conversations, I started building. Not a company. A prototype. Something that addressed the full problem, not just one piece of it. I brought it to RSA that year and showed it to a group of CISOs I'd been working with.
Their reaction was not what I expected. It wasn't "interesting idea." It was "Can we have this?"
That was the moment. This wasn't a side project. This was a company. The category it occupied didn't have a name yet, because nobody had built for the full scope before. We called it Autonomous Security Operations. And we started building Alaris.
The Category is Here
Autonomous Security Operations is not a feature set. It is not an AI add-on to your existing stack. It is a new architecture for how security operations gets done.
One platform. Seven stages. Full autonomy.
The question for every security leader is not whether this shift happens. It is whether you lead it or react to it.
David Colombo
Founder & CEO, Alaris
Globally recognized security researcher and advisor by 19. Advised major tech companies and European defense programs. As featured in Bloomberg, Forbes, and Reuters.
Frequently Asked Questions
What is Autonomous Security Operations (ASO)?
A new category of cybersecurity platform. One platform, all seven stages of security operations, fully autonomous. The human sets the strategy. The platform operates.
How is ASO different from an AI SOC?
Scope and architecture. AI SOC companies started at triage and are expanding stage by stage, adding separate agents onto existing toolchains. ASO was built from the ground up as one platform for all seven stages. One system, not seven bolted together.
Does ASO replace my SIEM?
Only if you want it to. ASO works with your existing SIEM. Over time, some organizations choose to consolidate. That's a choice, not a requirement.
What are the seven stages of security operations?
Detection Engineering, Alert Triage, Investigation, Threat Hunting, Containment and Response, Remediation, and Reporting.
Is an autonomous SOC the same as ASO?
Related, not identical. "Autonomous SOC" usually means AI automating some SOC functions. ASO requires all three: unified architecture, end-to-end autonomy, and full scope across all seven stages.
Do I still need security analysts with ASO?
Yes. ASO changes what they do, not whether you need them.
What size company needs ASO?
Mid-market to enterprise (500+ employees) and MSSPs. If your team is drowning in tool fragmentation or alert volume, you're a fit.
How does ASO work with my existing security tools?
It integrates with your current stack. SIEM, XDR, identity providers, cloud environments. No rip-and-replace required.